To decrypt configuration files, the unit uses the encryption key registered to it beforehand. The unit determines
the encryption status by checking the extension of the downloaded configuration file.
For details about encrypting configuration files, contact the appropriate person in your organization.
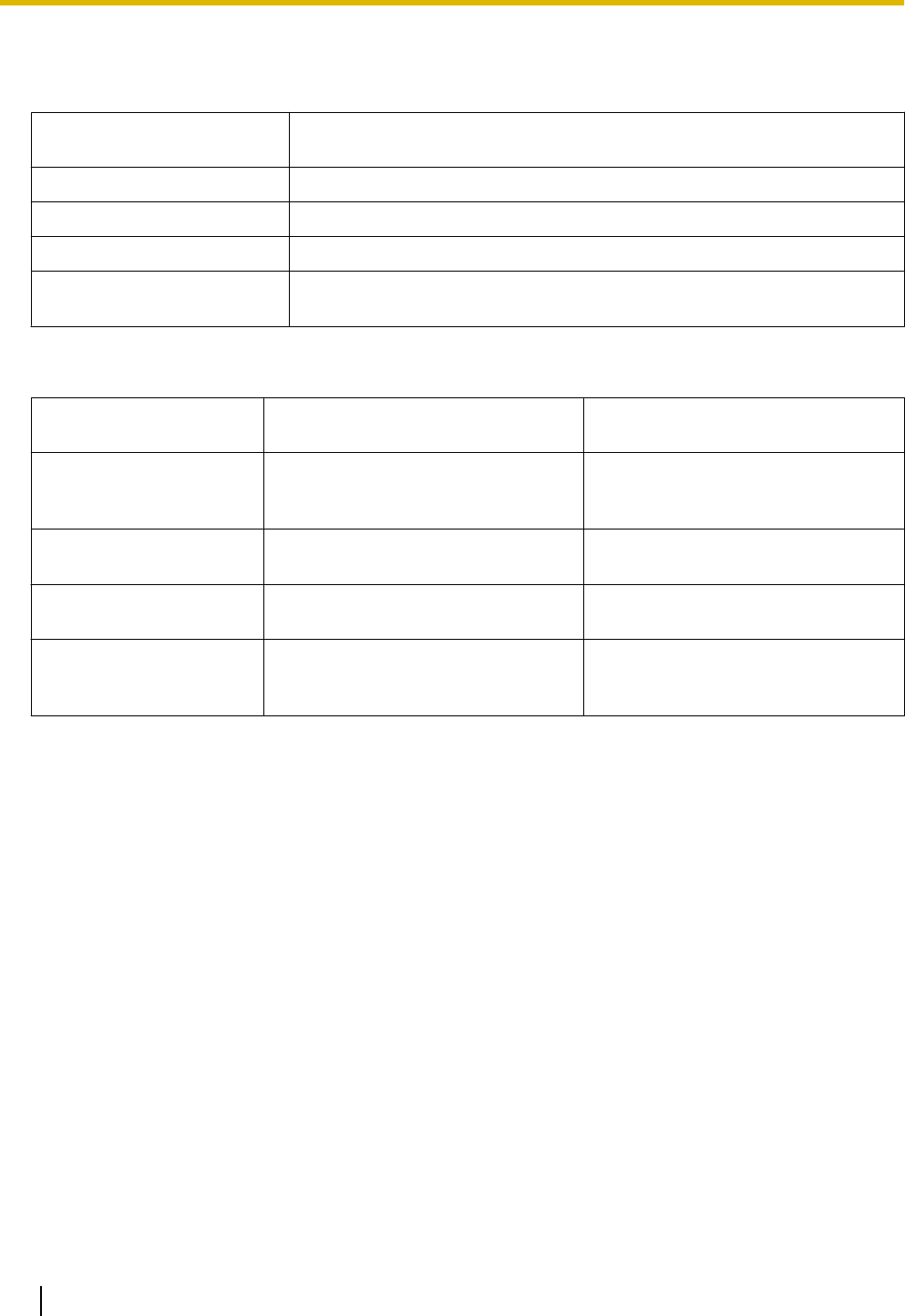
Extension of Configuration
File
Configuration File Parameters Used for Decrypting
".e1c"
CFG_FILE_KEY1
".e2c"
CFG_FILE_KEY2
".e3c"
CFG_FILE_KEY3
Other than ".e1c", ".e2c", and
".e3c"
Processed as unencrypted configuration files.
The extension ".cfg" should be used for unencrypted configuration files.
Comparison of the 2 Methods
The following table compares the characteristics for the 2 transfer methods.
Transferring Encrypted
Configuration Files
Transferring Configuration Files
Using HTTPS
Provisioning server load Light Heavy
(The server encrypts data for each
transmission.)
Operation load Necessary to encrypt data
beforehand.
Unnecessary to encrypt data
beforehand.
Management of
configuration files
Files must be decrypted and
re-encrypted for maintenance.
It is easy to manage files because
they are not encrypted on the server.
Security of data on the
server when operating
High Low
(Configuration files are readable by
anyone with access to the server.)
Moreover, there is another method: configuration files are not encrypted while stored on the server, and then,
using the encryption key registered to the unit beforehand, they are encrypted when they are transferred. This
method is particularly useful when several units are configured to download a common configuration file using
different encryption keys. However, as when downloading an unencrypted configuration file using HTTPS, the
server will be heavily burdened when transferring configuration files.
26 Administrator Guide Document Version 2010.03.15
1.1.6 Provisioning


















